WEBINAR
Identify AI Models in 3rd Party Apps
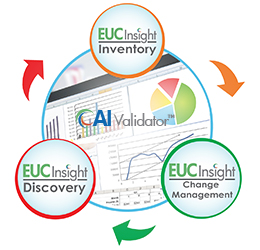
The use of AI models within third party applications is becoming increasingly common. Firms must have systems in place to identify these AI models and include them in their AI inventory for risk assessment and mitigation. Attend this webinar to learn how CIMCON’s AI Validator tool identifies AI Models in 3rd party applications, and how its EUC Insight platform provides a complete, end to end risk management platform for risk assessment, inventory, AI model validation and monitoring.
WHITE PAPER
Why EUC Risk Matters
The Business Case and Best Practices for End User Computing (EUC) Risk Management
Managing the enormous risks from End User Computing (EUC) applications is probably not on the top of the agenda for your C-suite. Nonetheless, you can be assured that they would care deeply if a material error related to EUCs were to occur or become public. It has cost a CEO their job.
Spreadsheet Risk Self Assessment
Complete a short survey to benchmark your business against spreadsheet risks.
Discover what we can do for you
Select your industry or use case below: